Protecting PACS and Medical Imaging: Steps to Cyber-Safety
Researchers offer several tips to help imaging facilities maximize their cybersecurity.
News of cybersecurity attacks usually surfaces in the context of credit card company breaches or social media infiltrations. But, more and more, healthcare – including radiology practices and departments – are falling victim to the same crimes.
According to group of investigators from Germany, though, there are steps imaging groups can take to safeguard themselves and avoid these debilitating incidents. The team, led by Marco Eichelberg, Ph.D., senior researcher with the OFFIS-Institute for Information Technology, published their recommendations in the Oct. 3
“Cybersecurity is a complex topic that requires significant effort to address, on different layers (physical, technical, and organizational). Hospitals, in general, and PACS operators, in particular, will have to address this topic, since healthcare is increasingly recognized as an important part of a society’s critical infrastructure that requires protection, including protection from cyber threats,” the team said. “Many of the building blocks for implementing cybersecurity are available today and just need to be planned, procured, deployed, and maintained.”
Related Content:
In 2019 alone, approximately 40 million people were affected by a healthcare data breach, and Black Book Research put a price tag of $4 billion on those attacks. For imaging centers and radiology departments, the main access point for outside invaders is, frequently, an outdated device or platform. In fact, a recent report from Palo Alto Networks, am enterprise security firm, determined that 83 percent of medical imaging devices are running on outdated software.
To help practices and departments fend off attacks, Eichelberg’s team outlined several recommendations that can put them on the right track.
Related Content:
Updates: Make sure all software and operating systems are current, and make use of firmware and virus scanners. When purchasing a new device or system, get a clear answer from the vendor about how and when they will provide security updates throughout the life of the product. In addition, be sure there is agreement on how those updates will be implemented. For example, opt to phase out old algorithms whenever possible, the team suggested.
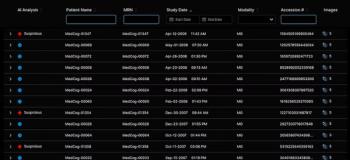
Virus scanners: Use virus scanners on all systems where they are permitted, placing high priority on any devices that are part of the hospital’s central IT infrastructure. Be sure to have a clear malware protection strategy for modalities and software-only products, such as RIS and PACS.
Access rights: Frequently, employees are the biggest security threat for a healthcare environment – and not because they are actively trying to be subversive. They just simply make mistakes. Consequently, its vital to work with the PACS vendor to establish a long-term strategy for implementing access rights, including user authentication on operation system and application level, as well as providing user context across network interfaces and application integration.
Encryption: Put TLS encryption in place for network interfaces with bi-directional authentication wherever feasible, and be sure that all central IT infrastructure systems support this. Encrypted network communication and audit trail support should be a requirement for any new device purchase to be made.
The team also examined the use of digital signatures as a safety precaution, but they stopped short of making a formal recommendation because too many unclarified issues around its use remain.
Overall, the team stressed, successful implementation of cybersecurity will require collaboration between users and vendors.
“Implementing some of the security measures described…is rather straightforward and can be performed by the user organization operating the PACS and medical imaging devices,” the team said. “There are, however, security measures that require a collaboration between the user organization and the vendors.”
For more coverage based on industry expert insights and research, subscribe to the Diagnostic Imaging e-newsletter
Newsletter
Stay at the forefront of radiology with the Diagnostic Imaging newsletter, delivering the latest news, clinical insights, and imaging advancements for today’s radiologists.